The Value of Recon
- Jul 25, 2022
- 4 min read
Reconnaissance is the first action in which a threat actor engages with a target and for our purposes can be defined as the use of openly available Internet sources of information to gain insight into an organization’s applications, services, technologies, people, and webpage relationships. In a nutshell, reconnaissance is nothing more than locating and analyzing publicly available sources of information about an individual or organization.
Now, you might be saying “so what, I don’t have any information out there that an attacker can use against me.” This is where in many cases, you are dead wrong! Performing reconnaissance on yourself or your organization is an important process that is often overlooked and is a great way to understand what information you are freely giving to potential attackers.
With the proliferation of social media and other online activities, a wealth of information exists today on the open internet that is perfectly legal for anyone to gain access to. In many cases gathering information from these public sources is all that is required to give an attacker everything they need to successfully profile an organization or individual in order to launch a successful social engineering or phishing attack. This is all done without the victim even being aware it is happening. Being aware of what kind of information that can be gathered about you from public sources can aide you or your security team in developing better defensive strategies.
So now you might be wondering how to perform this reconnaissance! Let us look at some open-source tools that you can use.
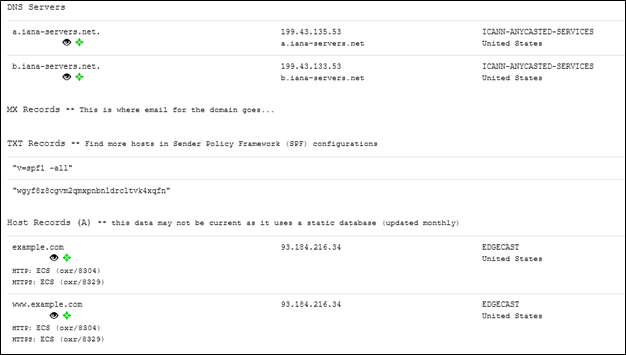
DNSDumpster is a free domain search tool provided by hackertarget.com that can discover hosts related to a domain. This is an essential tool as it allows you to quickly identify your attack surface. DNSDumpster is a passive reconnaissance tool in that it gathers information from open-source resources as opposed to directly querying your DNS servers.
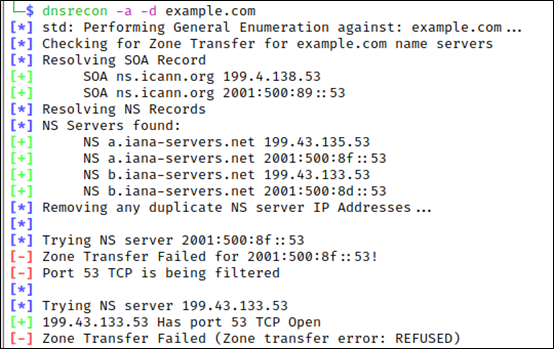
DNSRecon is a Python based tool allowing you to not only enumerate general DNS records but also check each listed NS (Name Server) record for zone transfers. Why is this important? Typically, a DNS server is configured to perform a zone transfer to and from trusted DNS servers. However, if your Name Servers are configured to allow zone transfers from anywhere, that means that anyone can perform a zone transfer and thereby download a copy of your entire DNS zone. This provides an attacker with a lot of information that they do not necessarily need to see.
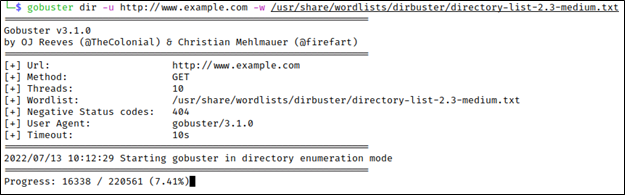
Gobuster and Dirbuster are both automated tools that can be used to check for common files and directories that may be running on a web server by attempting to brute force directory and file names. These tools are both similar however, Dirbuster does have the advantage of being able to perform a recursive search. They both work by using a wordlist and sends an HTTP GET request to the website and based on the response determines the likelihood of a file or directory existing on the site.
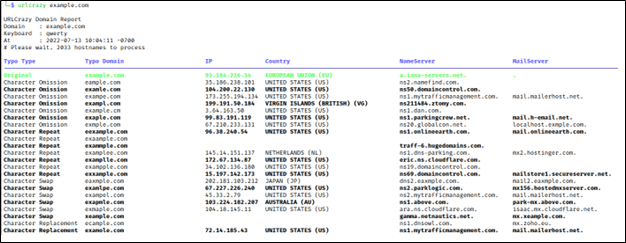
URL Crazy is a tool to test for domain typos or variations to look for things like typo squatting, where a lookalike domain name is used by an attacker for example www.google.com and www.gooogle.com. The goal in typo squatting is to make someone believe that the typo squatted domain is actually the legitimate domain in hopes that a visitor might reveal information they might not provide to a third party such as a user’s credentials.
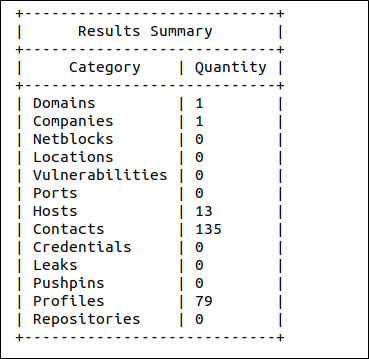
Recon-NG is a modular reconnaissance framework used to identify IP addresses and publicly accessible information about an organization using various search engines such as Shodan, Bing and Google. There are many modules available some of which are free to use, and some require a paid API key. Its interactive command line interface is similar to Metasploit and provides an incredibly powerful environment from which web-based reconnaissance can be performed. A word of caution, when running against shared IP addresses such as AWS or Azure, there is a strong likelihood that Recon-NG will resolve domains names to IP addresses that do not actually belong to you.
It is common for organizations to have publicly available files such as pdf, docx and xlsx to name a few. However, these files often contain sensitive information such as usernames, computer names and software applications in use at the organization that might be of value to a potential attacker. One such tool to assist in finding these files is PowerMeta.

PowerMeta is a PowerShell based tool that searches for publicly available files hosted on various websites using specially crafted Google and Bing searches. Any files found will be downloaded and analyzed by PowerMeta and any metadata will be extracted using Exiftool. You would be amazed the information you can find in these documents.
This is by no mean an exhaustive list, but it is a great starting point and aside from some subscription-based API’s, will cost next to nothing to get you started. Reconnaissance is absolutely something you should be doing. After all, malicious actors are performing this already so don’t you want to know what they know about you?