top of page
Brockton Point Solutions seamlessly integrates CrowdStrike’s Falcon platform

Blog
Latest Articles on Cyber security Trends


Cyber-Enabled Fraud and Phishing at Scale: Why the Human Layer Is Still the Fastest Way In
For all the advances in ransomware, cloud intrusion, and supply chain compromise, one old truth still holds: it is often easier to trick a person than to break a system.
2 days ago2 min read

AI-Powered Attacks and AI Security: Why Cyber’s New Arms Race Is Already Here
Artificial intelligence is no longer a future cybersecurity issue. It is a present-day force multiplier on both sides of the fight.
Apr 302 min read


The Latest Cyber Security Trends Executives Need to Watch in 2026
In 2026, cybersecurity is no longer just a technology issue. It is a business resilience issue, an operational continuity issue, and increasingly, a leadership issue.
Apr 225 min read


Identity Is the New Perimeter: Why the Smartest Attacks Now Start with Access
For years, cybersecurity was framed around protecting the network perimeter. Today, that model is fading fast. In modern environments built on cloud platforms, SaaS apps, remote work, APIs, and third-party integrations, the real perimeter is identity.
Attackers know that too.
Apr 12 min read


The Evasive Adversary: Why Modern Attacks Are Harder to See and Faster Than Ever
The 2026 CrowdStrike Global Threat Report describes a threat landscape defined by speed, trust abuse, and cross-domain intrusions. The defining shift is not a new class of attack, but a change in how adversaries operate.
Mar 176 min read

AI-Driven Threats and Defenses: How Artificial Intelligence Is Reshaping Cybersecurity
Artificial intelligence has moved from a supporting role in cybersecurity to a central force shaping both attacks and defenses. What once required time, skill, and manual effort can now be automated, scaled, and optimized by machine learning models often faster than security teams can respond.
Feb 199 min read


ISO 27001 in 2026: Why the Updated Standard Is a Board-Level Risk Management Tool
ISO 27001 has evolved from a technical security framework into a strategic governance instrument. With the transition to ISO 27001:2022 now complete, 2026 represents the first full operating year in which organizations are expected to run a modern, risk-driven Information Security Management System (ISMS) that aligns with today’s threat landscape, regulatory pressure, and stakeholder expectations.
Feb 43 min read


PCI DSS in 2026: Integrating Payment Security Into Enterprise Risk Strategy
PCI DSS remains a mandatory requirement for organizations that store, process, or transmit payment card data. However, in 2026, leading organizations are no longer treating PCI DSS as a narrow compliance obligation owned by IT or finance. Instead, it is increasingly positioned as a core component of enterprise risk management, aligned with broader security, governance, and resilience objectives.
Jan 283 min read


SOC 2 in 2026: From Compliance Exercise to Market Differentiator
SOC 2 has firmly evolved from a compliance milestone into a strategic trust signal for technology-enabled organizations. In 2026, a SOC 2 Type II report is no longer viewed merely as proof of security controls, but as evidence of organizational discipline, operational reliability, and sustained execution. For many customers, partners, and investors, SOC 2 has become shorthand for whether a company can be trusted to operate at scale.
Jan 223 min read


Brockton Point Solutions 2025 Year in Review: Navigating the Evolving Cybersecurity Landscape
As we close out 2025, the cybersecurity landscape has undergone dramatic transformations that have reshaped how organizations approach digital defense. At Brockton Point Solutions, we've been on the front lines helping our clients navigate these changes. We're taking this opportunity to reflect on the key trends that defined this pivotal year in cybersecurity.
Dec 21, 20258 min read

The Dark Side of AI: How Anthropic’s Admission Reveals the New Cyber Threat Reality
In a sobering revelation that should concern every cybersecurity professional, Anthropic has publicly admitted that hackers have successfully “weaponized” their AI tools to conduct sophisticated cyberattacks. This admission, detailed in their latest Threat Intelligence report, marks a pivotal moment in the evolution of cyber threats and offers a terrifying glimpse into how rapidly artificial intelligence is reshaping the threat landscape.
Oct 8, 20255 min read


Canada's Cybersecurity Outlook
Key Insights from the National Cyber Threat Assessment 2025–2026 The National Cyber Threat Assessment 2025–2026 (NCTA) from the Canadian Centre for Cyber Security outlines a stark reality: Canada is on the frontline of a rapidly evolving cyber battlefield. State-sponsored adversaries, cybercriminal groups, and hacktivists are targeting critical infrastructure, government, businesses, and individual Canadians at unprecedented speed and scale.
Sep 8, 20252 min read


New Cyber Threats Everyone Should Know About
Artificial Intelligence (AI) is everywhere now from the voice assistant on your phone to the chatbots on business websites. While AI makes our lives easier, it is also creating brand new ways for criminals to attack businesses and steal from consumers. These are not just upgraded versions of old scams, they are completely new threats.
Aug 20, 20256 min read


Maximizing Cybersecurity: Expert Tips for Risk Assessment Strategies
In today's digital world, cybersecurity is more important than ever. With increasing threats and sophisticated attacks, businesses must prioritize their security measures. One of the most effective ways to do this is through risk assessment strategies. Understanding your vulnerabilities and potential threats can help you create a robust defense system. In this blog post, we will explore expert tips for maximizing cybersecurity through effective risk assessment strategies. Whe
Aug 7, 20254 min read


Building Strong Security Awareness: User Training for Data Privacy
In today's digital world, data privacy is more important than ever. With increasing cyber threats and data breaches, organizations must prioritize security awareness among their users. Training employees on data privacy not only protects sensitive information but also fosters a culture of security within the organization. This blog post will explore the importance of user training for data privacy, effective training methods, and practical tips to build strong security awaren
Aug 7, 20255 min read


Stay Ahead of Cyber Threats: Comprehensive Cloud Security Solutions
In today's digital world, cyber threats are everywhere. Businesses of all sizes face risks that can lead to data breaches, financial loss, and damage to their reputation. As more companies move their operations to the cloud, the need for robust cloud security solutions has never been more critical. This blog post will explore various cloud security solutions that can help you stay ahead of cyber threats. We will discuss the importance of cloud security, the types of threats y
Aug 7, 20254 min read


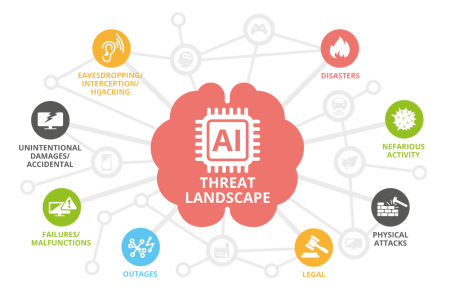
Critical Cybersecurity Elements in the AI Era
Securing the Intelligence Revolution The artificial intelligence revolution is reshaping every aspect of our digital landscape, from autonomous vehicles to financial trading systems. But as AI becomes more sophisticated and ubiquitous, it's creating an entirely new attack surface that cybersecurity professionals must understand and defend. Today, we'll explore the critical security challenges emerging in our AI-driven world and the strategies needed to address them.
Aug 7, 20255 min read


Top Cybersecurity Risks for Business Owners in 2025
As technology continues to evolve, so do the tactics of cybercriminals. In 2025, the digital landscape is rife with opportunities and risks for businesses of all sizes. Here are the top cybersecurity concerns every business owner should prioritize to safeguard their operations, data, and reputation.
Jan 5, 20253 min read


Cyber Security Risks to Small Businesses
Cybersecurity is critically important for small businesses, even more so than for larger corporations, due to several unique challenges and vulnerabilities that small businesses face.
Mar 5, 20242 min read


Securing the Future: Cybersecurity in 2024
As we step into 2024, the cybersecurity landscape continues to evolve rapidly. It is crucial for both individuals and organizations to stay informed of the latest developments to safeguard against ever-evolving and complex cyber threats.. Here’s a look at some of the key cybersecurity trends in 2024
Jan 4, 20242 min read
bottom of page